Collaboration is the process where individuals or teams work together toward a common goal, combining skills and efforts to achieve outcomes that are difficult to accomplish alone. It involves active communication, coordination, problem-solving, and shared responsibility, ensuring everyone is moving in the same direction. For organizations, effective collaboration is essential.
When teams work well together, they reduce duplication of effort, make faster and more informed decisions, and respond more quickly to challenges. Strong collaboration also increases engagement, as employees feel heard, supported, and part of a shared mission.
Improving collaboration starts with giving teams what they need to work effectively together. This includes providing the right tools and resources, establishing clear roles and responsibilities, and promoting open, transparent communication that keeps everyone aligned. Equally important is fostering a culture of trust, knowledge sharing, and shared responsibility, so members feel confident sharing their best ideas.
With proper guidance, training, and streamlined systems, collaboration becomes a natural, productive part of daily work instead of a challenge. These foundations set the stage for more targeted strategies, such as defining goals, assigning tasks based on strengths, building a safe environment where people can speak openly without fear of criticism, and promoting creative problem-solving to elevate teamwork to its fullest potential.
By intentionally implementing the following collaboration strategies, organizations create an environment where teams can work efficiently, adapt quickly, and deliver stronger results. It is about enabling people to connect, share, and contribute their best work toward a common purpose.
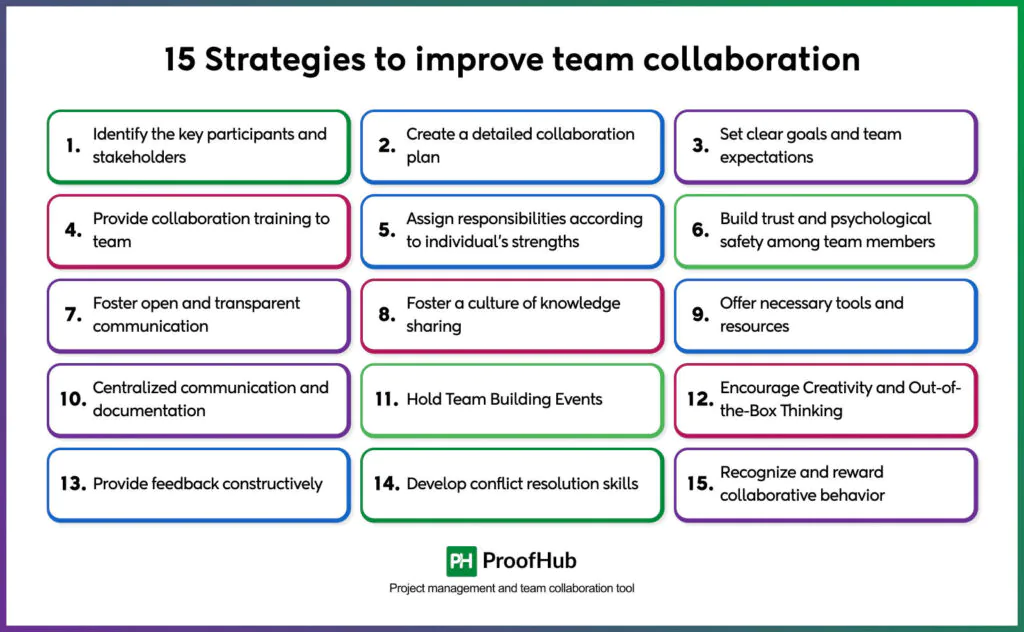
1. Identify the key participants and stakeholders
Identifying key participants and stakeholders shows who is involved in the work and who is affected by it. This makes it easier to understand everyone’s roles, needs, and expectations. As a result, teams coordinate better, reduce confusion, and work more smoothly with each other and with anyone else who has a stake in the outcome.
It’s important to understand the difference between key participants and stakeholders.
- Key participants are directly involved in the day-to-day work—they make decisions, carry out tasks, and take responsibility for results.
- Stakeholders, on the other hand, may not be involved in the actual work but are still connected to the outcomes. They may be affected by results, interested in the project, or able to influence its direction.
To identify key participants, look at job roles, team structure, workflows, and areas of expertise. This shows who has specific responsibilities, knowledge, or authority. Identifying stakeholders requires a different approach: scanning the environment, assessing who might be impacted, mapping influence networks, or analyzing communication patterns. This helps uncover groups or individuals who may not be evident at first—such as external partners, interest groups, or outside decision-makers.
There are many methods to help with this process. For example:
- The power-interest grid, developed by Ackerman and Eden, maps stakeholders by their influence and interests.
- The salience model, developed by Mitchell, Agle, and Wood in 1997, ranks stakeholders by power, legitimacy, and urgency.
- Other approaches include mapping influence networks, studying cultural dynamics, or planning scenarios.
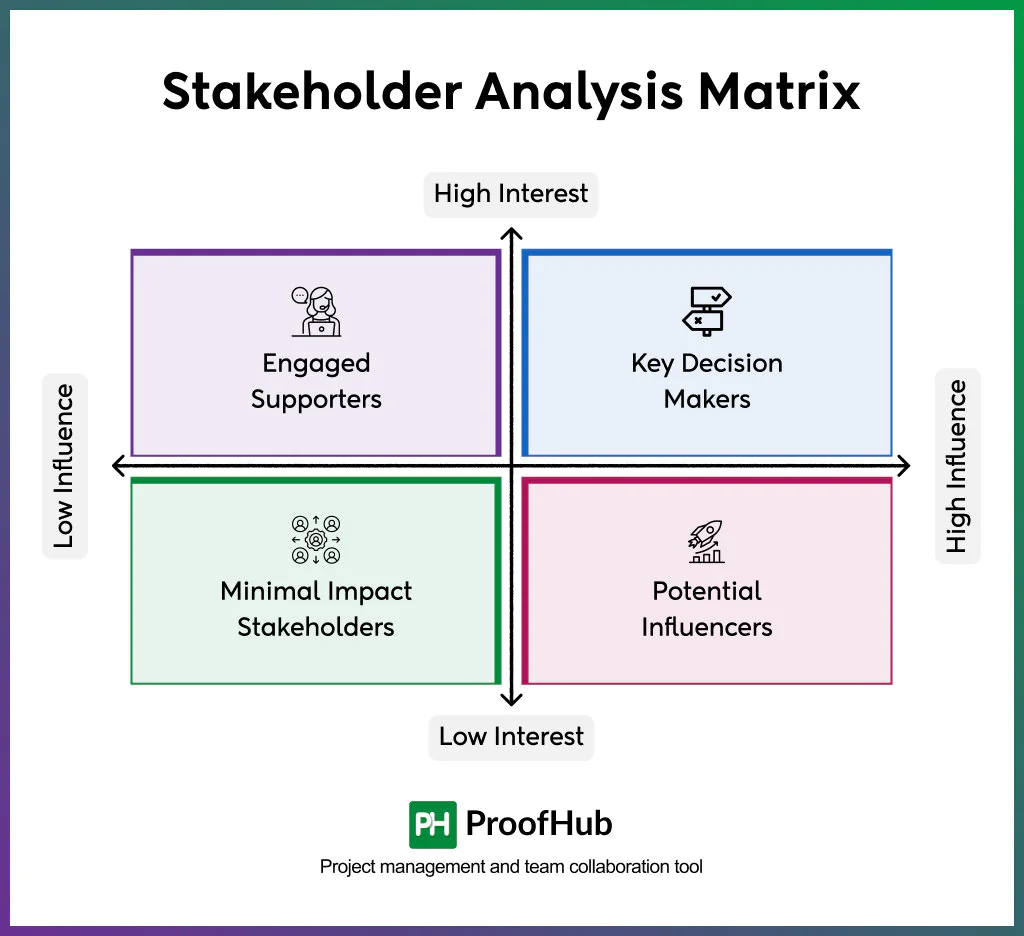
Some methods work for both participants and stakeholders, such as resource dependency analysis (a technique for understanding how much groups rely on each other’s resources) or a modified power-interest grid. Others are more specific. For example, role analysis (a method for clarifying responsibilities within a team) works best for participants, while environmental scanning is better for stakeholders.
Doing this well improves collaboration: it clarifies responsibilities, reduces silos, tailors communication, guides resource sharing, and supports risk management. It also ensures the team’s work stays aligned with broader goals.
Moreover, stakeholders and roles change as projects evolve or organizations shift. That’s why the process should be reviewed and updated regularly.
2. Create a detailed collaboration plan
Creating a collaboration plan is a practical strategy to improve how teams work together. Instead of relying solely on random teamwork and casual cooperation, a collaboration plan provides teams with a structured framework for communicating progress, coordinating work, and moving toward shared goals more efficiently. Most teams know they need meetings and goals to stay aligned. However, hidden obstacles, like unspoken rules, mismatched collaboration styles, or small handoffs that go unnoticed, often cause a project to derail. A strong collaboration plan anticipates these hidden friction points and builds safety guardrails around them.
The first step in building a practical collaboration plan is reviewing how work actually happens. This means going beyond the ideal process flow to map what actually occurs, where delays occur, where communication breaks down, and which tasks aren’t even tracked. Teams can create a simple “Friction Map” to capture these insights: list pain points, their impact, and who’s affected.
At the same time, it’s helpful to surface individual working styles by asking questions like: “What conditions help you do your best work?” This reveals mismatches that may not be obvious, such as one person needing long stretches of quiet while another thrives on quick, high-energy exchanges.
Once those patterns are visible, the collaboration plan should establish communication frequencies and decision protocols that reduce friction. For example, replace repetitive status meetings with short asynchronous updates where each person shares what they did, what they’re stuck on, and what they need help with.
For urgent issues, quick instant messages work well—but for deeper decisions, set up short written or recorded summaries to clarify what was agreed upon and why. When disagreements arise, use a simple tie-breaker process: people share their views in writing, and a rotating decider makes the call quickly. These kinds of lightweight systems reduce confusion while respecting focus time.
Example of collaboration plan:
| Description | Frequency | Channel (ProofHub) | Audience | Owner |
| Daily status logs | End of each workday | Team Discussion Board | Project team | Each team member |
| Task-specific updates | As tasks progress | Task Comments | Assigned members + related teammates | Task assignee |
| Issue reporting & quick clarifications | Immediately after identified | Chat | Project manager + project team | Any team member |
| Key stakeholder updates | Bi-weekly or project phases | Announcements | Key stakeholders | Project owner / PM |
| Milestone documentation | Upon completion | Notes | Project team + stakeholders | Project owner / PM |
| Organization-wide announcements | As needed | Announcements | Entire organization | Project owner / leadership |
| Knowledge sharing / learnings | Ongoing | Notes / Discussions | Project team & new members | Any contributor |
| Brainstorming & idea exchange | At project start or review cycles | Discussions | Project team | Facilitator / Team lead |
It’s equally important to check how the team is feeling about collaboration, not just what it’s producing. Every couple of weeks, ask team members to rate how clear their priorities are, whether their workload feels manageable, and how well tensions are being resolved. Over time, these quick check-ins help spot issues early and prevent long-term burnout. If a specific issue keeps surfacing, like unclear handoffs or recurring meeting fatigue, log it and dedicate time in the next sprint to fix it.
3. Set clear goals and team expectations
Setting clear goals and team expectations reduces uncertainty and friction among team members. This strategy operates on the fundamental principle that ambiguity is the enemy of effective collaboration. Establishing clear goals with a clear understanding of expectations, both at the individual and team levels, helps you create predictable frameworks that enable team members to coordinate seamlessly.
A good way to set these goals is to follow the SMART framework—make sure goals are Specific, Measurable, Achievable, Relevant, and Time-bound. For example, instead of saying “Improve onboarding,” define it as “Reduce time-to-productivity for new hires from 30 days to 20 days within this quarter.” When goals are framed like this, progress becomes trackable, alignment becomes easier, and decisions become clearer. It also makes it easier for team members to prioritize, delegate, and take ownership without constant oversight.

Then comes team expectations. These are the rules or standards you set for how people interact, make decisions, communicate, and resolve conflicts. These expectations serve as an operational norm for sharing information and help reduce friction among team members. It also makes it easier for team members to prioritize, delegate, and take ownership without constant oversight.
Clarity in both goals and expectations creates shared mental models, enabling everyone to interpret the work the same way and understand how their part fits into the whole. This eliminates the subtle misalignments that often derail collaboration. It also helps reveal dependencies. When people understand how their work feeds into others’, they naturally begin to check in on time, flag risks earlier, and plan their tasks with teammate’s dependence in mind. That builds mutual accountability through shared ownership.
4. Provide collaboration training to the team
Collaboration training is a structured learning approach that equips individuals and teams with the necessary skills, frameworks, and tools to work together more effectively. It focuses on enhancing communication clarity, defining roles, managing conflicts, fostering emotional intelligence, and leveraging collective problem-solving to improve team dynamics and outcomes.
Many teams assume they’re already doing well—especially when it comes to communication. But in reality, poor communication is one of the most common reasons collaboration fails. We often act without noticing the assumptions behind how we talk or work with others. Problems arise when people have different communication or decision styles.
Start by understanding how your team works today. Are there gaps? Maybe people don’t speak up in meetings, or maybe teams don’t trust each other. Look at the organization, your team, and even individual behavior. Talk to people individually and in groups to learn more.
Once you spot the problems, design training programs around them. If people communicate in very different ways, help them recognize those differences—for example, direct vs. indirect communication, or written vs. spoken preferences. Then teach strategies such as confirming understanding, paraphrasing key points, and choosing the right channel based on the message and the person.
If teams don’t trust each other, run exercises that require them to rely on one another—such as solving a complex task in which each member holds a piece of the solution, or rotating leadership in group problem-solving sessions. These exercises create safe situations where people see each other’s reliability and build respect.
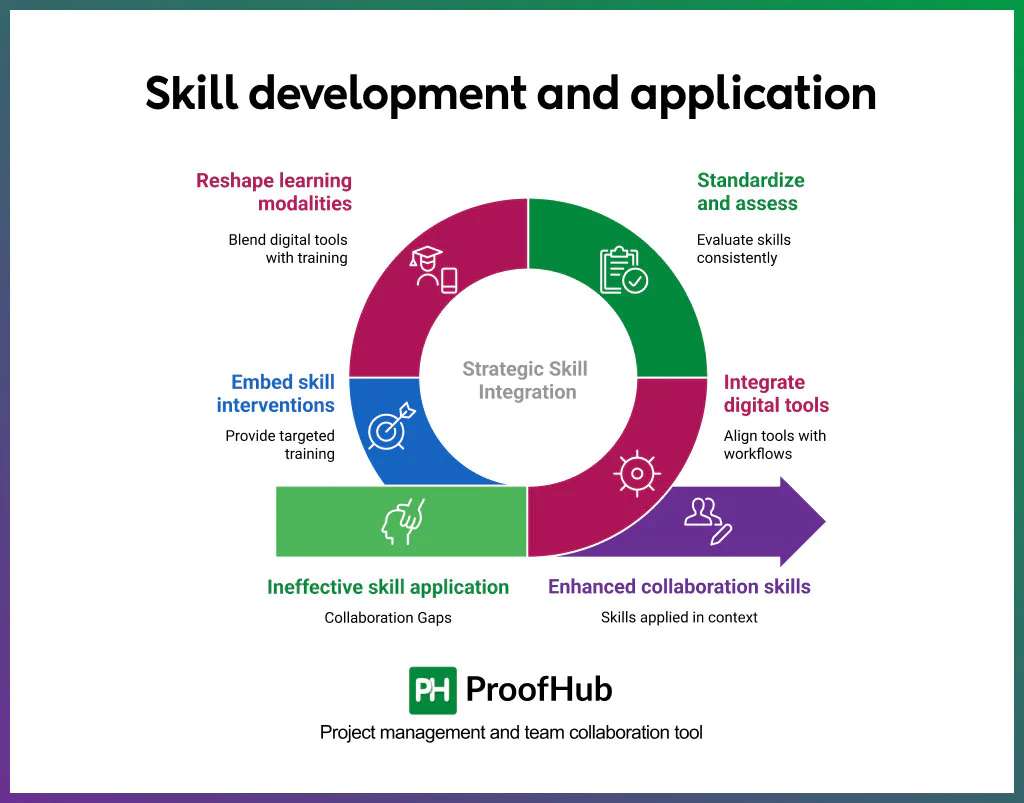
You can take it further by giving your team practical tools. For instance, use a shared project management tool like ProofHub to centralize the flow of information. For decisions, agree in advance on methods, such as voting, manager’s approval, or consensus. For conflicts, adopt a simple protocol like “pause, clarify, propose” to keep discussions constructive and moving forward.
A systematic literature review published in the International Journal of Human–Computer Interaction (2025) titled “Collaborative Skills Training Using Digital Tools: A Systematic Literature Review,” states that delivering instructions on how to collaborate during a computer-based collaborative task improves performance and task conflict regulation. In other words, structured guidance and the right tools make collaboration training far more effective than leaving teams to “figure it out” on their own.
Good collaboration training improves efficiency and performance. Teams avoid repeating work and understand how their actions affect others. Most importantly, they feel safe being honest, asking for help, and learning from mistakes. That’s when teamwork becomes truly effective.
5. Assign responsibilities according to individual’s strengths
Assigning roles based on strengths means matching people’s talents and working styles to their responsibilities. Instead of fixed roles, shape responsibilities around what people do best. For example, instead of rotating who leads client presentations, give that task to someone who thrives in high-stakes communication and relationship-building.
Too often, teams are structured by circumstance, with people promoted or assigned roles based solely on seniority or technical skills. While those matters exist, they can create a gap in teamwork. For instance, the top-performing salesperson may not make an effective sales manager if they lack coaching and people-management abilities. This mismatch can lead to friction, missed tasks, or poor morale, frustrating the team and hurting collaboration.
To assign the right responsibilities, distinguish between being great at your own tasks and the ability to support and coordinate with others. Someone might solve problems well on their own but struggle to explain their reasoning to teammates. Assigning them a mentoring or leadership role could backfire—not because they lack competence, but because their strengths don’t align with the role.
To avoid these pitfalls, use a simple strengths-to-responsibilities matching process. Start with a short self-assessment where team members reflect on their functional strengths, working styles, and comfort zones in collaboration—whether that’s initiating discussions, handling details, or resolving conflicts.
One practical way to identify individual strengths is through a popular assessment called CliftonStrengths, which helps people surface their natural ways of thinking, relating, and getting work done. It’s widely used and gives teams a shared vocabulary to assign roles more intentionally. But no tool replaces judgment—it should be a starting point, not a substitute for conversations, context, or evolving team needs.
6. Build trust and psychological safety among team members
Trust and psychological safety are the practical tools that make real collaboration possible. Trust is the foundation; psychological safety sits on top of it. When trust is built systematically, safety becomes the default. And when safety is present, people can raise concerns, share ideas, and ask questions without fear of judgment or repercussions.
But safety doesn’t emerge just because leaders encourage openness. Teams need visible structures that make candor normal and expected. Blameless post-mortems, for example, shift the focus from blame to learning by examining failures without targeting individuals. Organizations like NASA and Bridgewater institutionalize this through “issue logs” that capture mistakes in real time—not to shame, but to detect patterns early. Even small nudges help: Slack bots that ask, “Who haven’t we heard from?” or meeting tools that highlight airtime imbalances quietly build habits of inclusion.
The results are tangible. Teams with higher psychological safety iterate faster, surface risks earlier, and make stronger decisions. Gallup found that employees who feel their opinions count contribute to a 27% reduction in turnover, 40% fewer safety incidents, and a 12% rise in productivity.
Leaders play a decisive role in whether this environment takes hold. Not by cheerleading from the sidelines, but by going first, modeling candor, sharing missteps, and inviting pushback. At Amazon, managers begin reviews by admitting personal failures. At SpaceX, any engineer can pause a launch through a “no-fault” channel. At IBM, employees who challenge assumptions and prevent costly errors are publicly recognized rather than quietly dismissed. These practices make vulnerability visible, setting a standard the whole team can follow.
7. Foster open and transparent communication
Fostering open and transparent communication can improve collaboration by reducing misunderstandings, easing access to information, and promoting a shared understanding among teams. In practical terms, it means replacing the selective, need-to-know basis infrastructure of information sharing with a system that keeps everyone—across levels, roles, and functions—on the same page. However, it is not about flooding people with information they don’t need. Hence, this shift to open and transparent communication practices requires strategic implementation.
One way to think about it is to design your collaboration plan for cognitive aid rather than for information broadcasting. Teams often confuse transparency with more communication, creating unnecessary information overload. In fact, a study by SIS found that 77% of employees report spending two or more hours per week wading through unwanted communications—distractions that make finding the relevant information much harder. The real goal is to ensure the right people have the right information at any given time.
Teams can do this well by designing intentional channels, protocols, and expectations for open communication. This includes making asynchronous updates the default for status reporting and project progress—using shared documents or project management tools that everyone can reference, rather than relying on meetings or private threads. It also means structuring meetings around decision points or key blockers, not updates that can be read.
Teams should define what kinds of communication belong in which channel (e.g., decisions go in project logs, quick updates in chat, longform feedback in docs) and make those norms explicit. Transparency should be searchable—not ephemeral—so institutional knowledge doesn’t get buried in inboxes or Slack history. Finally, team leads should model the behavior: narrate the context behind decisions, make tradeoffs explicit, and document learnings where others can benefit from them.
Additionally, transparency helps improve decision velocity and quality. This happens by collapsing the layers between information and decision-makers. When teams have access to relevant data early, customer feedback, project blockers, and performance metrics, they don’t have to escalate or wait for top-down clarification. Instead, they can course-correct in real time.
Research on psychological safety and behavioural integration shows that when team members are encouraged to surface unfiltered data—even when it’s inconvenient—it creates a more adaptive, truth-seeking decision culture. By embedding transparency into planning, retrospectives, and postmortems, teams can continuously refine their decisions based on firsthand signals rather than filtered interpretations. The key is to treat transparency as infrastructure for better judgment—not a substitute for it.
8. Foster a culture of knowledge sharing
Creating a culture of knowledge sharing improves collaboration by structuring how information flows across the organization. When knowledge is treated as a shared resource, teams move from individual efforts to collective problem-solving. This change in mindset reduces dependency on specific people as solution providers. Instead of waiting to find the right person, individuals can access knowledge from a shared system of understanding—through documentation, open channels, or norms that encourage exchange.
Teams operate within a common context by sharing knowledge. They have complete understanding of how decisions were made, what’s been tried, and where pitfalls occurred—and engage more productively. Meetings and brainstorming become about building on insights, not catching up or repeating mistakes. This reduces misalignment, redundant work, and the coordination efforts that usually slow teams down. It also fosters healthy interdependence: a teammate relying on another to think out loud helps everyone view problems more holistically.
Shared ownership also makes collaboration feel less like negotiation and more like joint problem-solving. When knowledge flows across levels and roles, it weakens hierarchies that restrict input. Junior members can reference past learnings; cross-functional peers can understand constraints; new hires don’t start from zero. The team gains leverage with every piece of shared knowledge.
But fostering this culture takes more than encouraging documentation. It requires surfacing the correct information at the right moment. In practice, this means redesigning rituals such as reflection sessions (retrospectives), demos, and onboarding to teach each other what they’ve learned. Reward behaviors that prioritize clear, contextual knowledge sharing over speed or siloed output. When knowledge sharing becomes a cultural default—thinking and learning together—it makes teams resilient, responsive, and ready to solve problems as one.
9. Offer necessary tools and resources
Give your team the right tools and resources to collaborate effectively. Without them, even the most motivated people end up working in silos, chasing status updates, or duplicating each other’s efforts. The right tools don’t just support work—they shape how it gets done. They influence whether communication feels seamless or scattered, whether accountability is clear or constantly questioned, and whether projects move forward with momentum or stall in confusion.
This is why tool choice is not just an IT decision but a leadership one. Tools, when chosen thoughtfully and integrated into daily workflows, become part of the organization’s operating system. They reduce noise by centralizing information, prevent mistakes by keeping responsibilities visible, and make knowledge easy to find long after the project is done. In effect, they turn collaboration from a matter of coordination into a predictable, repeatable practice.
Take ProofHub, for example. It acts as a comprehensive platform that replaces the patchwork of spreadsheets, emails, and scattered chat threads with a single source of truth. Teams can build project boards to map out tasks, set deadlines, and assign owners, so accountability is always visible. Discussions tied directly to tasks keep context intact, no scrolling through inboxes or Slack history to piece things together. File versioning ensures everyone works from the latest version of the document, avoiding the classic “which file is final?” problem. And automated reminders surface deadlines without managers having to chase updates, freeing them to focus on higher-value leadership tasks.
The difference may seem subtle at first—one less email here, one less status meeting there—but over weeks and months, these efficiencies compound. A clear system for collaboration doesn’t just save time; it improves decision-making, reduces stress, and builds a culture where people can trust that the work in front of them is the real work that matters.
10. Centralized communication and documentation
Centralizing communication and documentation is one of the most effective ways to eliminate confusion, reduce duplication, and keep teams aligned—especially in hybrid or cross-functional environments. When conversations, decisions, updates, and resources are scattered across tools, inboxes, and personal threads, critical information gets lost or misunderstood. A centralized system brings all of this into one accessible and consistent space.
The goal isn’t just to reduce noise—it’s to make context easy to find and share. Without that, collaboration suffers. Teams spend more time searching than executing. People miss essential changes. Priorities get misinterpreted. Worse, decisions are repeated because the previous rationale was never recorded in the first place.
Centralization doesn’t require a single tool, but it does require agreed-upon rules. Decide where different types of communication live. For example:
- All project updates go into a shared project board.
- All key decisions are documented in a living doc or tool like Confluence or Notion.
- All real-time conversations happen in a designated Slack or Teams channel, not private DMs.
- All reference documents are stored in a shared drive, not scattered across emails.
This approach reduces cognitive load. When everyone knows where to look—and where to contribute—collaboration becomes faster and more confident.
A centralized system also makes onboarding and cross-team work easier. New team members can ramp up faster by reviewing key threads, recorded decisions, and past deliverables without having to chase down someone for context. Cross-functional collaborators don’t need to ask where things are—they’re already documented in a shared space.
Of course, centralized doesn’t mean “cluttered.” Too many channels, untagged messages, or unorganized files can make centralization just another source of overwhelm. To avoid this, assign a small group or rotating owner to maintain the system.
An effective system should also balance synchronous and asynchronous collaboration. Not all decisions need a meeting. Use shared docs for idea gathering, quick status updates, or decision proposals. This gives people time to think and contribute to their schedule, reducing the pressure of live discussions and allowing better input from quieter voices.
Finally, reinforce the system through usage, not rules. When team leads consistently document key takeaways, reference shared notes in meetings, and nudge others toward the central space, habits shift naturally.
The payoff is fewer repeated questions, faster decision-making, easier collaboration across teams, and reduced burnout from context-switching. Centralizing communication and documentation doesn’t slow things down—it gives people the clarity and focus they need to move faster with confidence.
11. Hold Team Building Events
Team building events are often dismissed as optional or superficial—but when designed with intent, they serve as a core driver of collaboration. They build the foundation for trust, communication, and problem-solving across all types of teams—remote, hybrid, or working in the same place.
Strong workplace collaboration isn’t built on tools or processes alone. It depends on team relationships—how well people understand one another, anticipate needs, and feel safe raising concerns or ideas. Team building accelerates these relationships by offering shared experiences that go beyond task execution. When people know and trust one another, coordination feels lighter, conflict becomes more constructive, and creative ideas surface more freely.
But not all team building delivers results. Generic games or “forced fun” can feel awkward or counterproductive. The key is to design experiences that match your team’s context, challenges, and growth stage.
Newly formed teams benefit from casual mixers or storytelling exercises that reveal personal backgrounds and working styles.
Distributed teams need structured virtual challenges that mimic real collaboration under constraints—such as timed escape rooms or cross-time-zone problem-solving games.
Teams emerging from conflict or burnout gain more from reflective sessions that bring up frustrations, clarify values, and reset communication patterns.
The best team-building activities consistently do three things:
- Surface hidden strengths and styles. Activities that call for different kinds of thinking reveal who thrives in which situations, helping teams self-organize more effectively in real work.
- Normalize vulnerability and disagreement. Practicing light conflict in a safe context builds confidence to tackle real disagreements constructively.
- Reinforce shared identity. Celebrating achievements or creating group rituals reminds people they’re part of something larger than individual key performance indicators (KPIs).
Embedding structured debriefs after each activity multiplies their impact. Asking “What worked? What surprised us? What can we apply to our day-to-day?” turns entertainment into actionable insight. Without this reflection, much of the value is lost.
Crucially, team building should not be relegated to a once-a-year offsite. Micro-rituals—like 15-minute check-in rounds, rotating coffee chats, or peer recognition moments—maintain connection throughout the year without disrupting work. These “small doses” build a lasting baseline of trust and collaboration.
Budgets and logistics aren’t barriers. Low-cost or no-cost formats—such as collaborative board games, joint volunteer projects, “teach a hobby” sessions, or storytelling circles about past wins—can be just as powerful as expensive retreats. What matters is relevance and consistency, not price.
When approached with intention, relevance, and frequency, team building delivers more than morale. It improves decision-making speed, shortens conflict resolution cycles, and strengthens cohesion
12. Encourage Creativity and Out-of-the-Box Thinking
Creativity fuels collaboration by opening new pathways for solving problems that rigid processes alone cannot address. When teams are encouraged to think beyond the obvious, they not only generate fresh ideas but also challenge assumptions that may be limiting progress. Out-of-the-box thinking creates a sense of possibility—problems are no longer seen as fixed constraints but as opportunities for invention.
This mindset directly enhances team collaboration. Instead of converging too quickly on the safest solution, members bring forward diverse perspectives, testing and refining each other’s ideas. Brainstorming sessions, design sprints, or casual idea exchanges turn into spaces where imagination is valued alongside practicality. The result is not chaos, but a more balanced approach where creativity and execution work hand in hand. Teams align around ideas they feel are co-owned, which strengthens both buy-in and momentum.
Fostering creativity also reduces the fear of being wrong. When leaders make it safe to propose unconventional ideas, even if they don’t work out, teams develop psychological resilience. A “failed” experiment becomes a source of collective learning rather than wasted effort. This builds trust and encourages members to contribute more freely, knowing their input will be respected.
Practically, encouraging out-of-the-box thinking involves creating deliberate structures for creativity. For example, setting aside time for ideation before decision-making, rotating facilitation roles to bring different voices forward, or running “what if” exercises to stretch the team’s imagination. Recognition also matters: celebrating not just successful ideas but the courage to propose bold ones reinforces the cultural value of creativity.
When creativity becomes embedded into team routines, collaboration feels less like following a script and more like co-creating the future. Teams that think freely and experiment together stay adaptive, inventive, and motivated—qualities that are indispensable for long-term success.
13. Provide feedback constructively
Feedback is one of the most powerful tools for improving collaboration, yet it often becomes a source of tension when delivered poorly. Constructive feedback shifts the focus from blame to growth, ensuring that individuals feel supported rather than judged. The goal is not simply to point out what went wrong, but to guide teammates toward better outcomes while preserving trust and morale.
When feedback is constructive, it strengthens collaboration by keeping communication open and respectful. Team members become more willing to share progress, admit difficulties, and ask for help, knowing that feedback will be framed as a path forward rather than a personal attack. This creates a healthier dynamic in which accountability and empathy work together rather than in conflict.
A key part of giving constructive feedback is clarity. Instead of vague comments like “this isn’t good enough,” effective feedback highlights specific behaviors, explains their impact, and suggests practical alternatives. Equally important is timing—feedback delivered promptly, while the context is fresh, allows people to adjust quickly and prevents minor issues from escalating into bigger problems.
Tone also matters. Feedback is most impactful when expressed with respect and genuine intent to help. Phrasing observations in terms of outcomes (“the deadline slipped, which delayed testing”) rather than judgments (“you’re unreliable”) keeps the focus on work rather than personality. Inviting dialogue—“How do you see it?”—further strengthens the feedback loop by ensuring it is two-way rather than top-down.
Constructive feedback should not only highlight areas of improvement but also recognize strengths. Balancing critique with appreciation reinforces what individuals are doing well and motivates them to continue. This balance creates a culture where feedback is not feared but welcomed as part of continuous improvement.
When teams master the art of constructive feedback, collaboration becomes more fluid and resilient. Challenges are addressed directly without damaging relationships, and growth is seen as a shared journey. In this way, feedback evolves from a corrective tool into a collaborative practice that pushes the entire team forward.
14. Develop conflict resolution skills
Developing conflict resolution skills is an essential part of effective collaboration. Disagreements in a team are inevitable. When diverse perspectives and strong ideas collide, friction can arise. Left unchecked, these tensions can damage trust, slow progress, and create an unhealthy work environment. But when handled well, conflict can actually sharpen thinking, strengthen relationships, and lead to better decisions.
Constructive conflict resolution begins with recognition. Leaders and team members alike need to notice early signs of tension rather than waiting for issues to escalate. From there, the focus should be on understanding the underlying concerns rather than just reacting to surface-level disagreements. This requires active listening, patience, and a willingness to see the situation from multiple viewpoints.
Equally important is creating a safe and neutral space for dialogue. Conversations about conflict should emphasize respect, openness, and solution-seeking rather than blame. Clear communication—where each person feels heard and understood—forms the foundation for resolution. Practical techniques such as setting ground rules for discussions, asking clarifying questions, and summarizing what’s been said help keep conversations constructive.
Finally, conflict resolution isn’t about producing winners and losers. It’s about finding common ground and making decisions that balance the needs of individuals and the team. When team members build these skills, they not only resolve disputes more effectively but also grow more resilient and cohesive. Instead of fearing conflict, they learn to use it as a catalyst for stronger collaboration.
15. Recognize and reward collaborative behavior
Collaboration thrives when it’s not only expected but also recognized and rewarded. Without deliberate reinforcement, collaborative efforts often go unnoticed, while individual achievements—especially those tied to visible outputs—take center stage. This imbalance sends the wrong message: that going solo gets the credit, while helping others is extra.
Recognizing collaborative behavior doesn’t require grand gestures or expensive programs. It starts by identifying what “good collaboration” actually looks like within your context. Is it mentoring a new teammate? Sharing early feedback to unblock someone else’s work? Volunteering for cross-functional projects? These actions need to be named, valued, and reinforced consistently.
One effective practice is to make collaboration visible during regular rituals. For example:
In sprint retrospectives, include a moment to highlight who helped you get unstuck.
In team meetings, create space to shout out those who went beyond their direct responsibilities to support others.
In performance check-ins, ask: “How have you contributed to others’ success?” and “Who supported your work this quarter?”
These touchpoints build a culture where collaboration becomes part of performance, not just personality.
Equally important is how you reward it. Public praise is powerful when it’s specific. Saying “Thanks for collaborating” is vague. Instead, say:
“I appreciated how you jumped in to test the new feature even though it wasn’t part of your task list—it saved the dev team a full day.”
This level of detail reinforces exactly what behaviors are valued.
You can also tie collaboration into existing recognition systems. For instance:
Adjust peer-nomination programs to include categories like “Best cross-functional collaborator.”
Include team-based goals in incentive structures, where the reward depends on shared progress, not just individual metrics.
Use shared dashboards to highlight collective contributions—not just who closed the most tickets or tasks.
For longer-term impact, align career progression frameworks with collaborative behavior. If promotions are based solely on individual output, people will optimize for self-interest. But if roles and raises reflect contributions to team outcomes, mentorship, or cross-team enablement, you encourage a broader sense of ownership.
Recognition can also be informal and frequent. A dedicated Slack or Teams channel where teammates can acknowledge support in real-time helps reinforce collaborative values without formal overhead.
Importantly, recognition must be inclusive. If only vocal contributors or those in visible roles receive praise, others will disengage. Pay attention to behind-the-scenes enablers, support staff, or those who quietly hold the team together. Leaders should actively seek input from peers to surface contributions that go unnoticed.
By consistently recognizing and rewarding collaborative behavior, teams send a clear message: supporting one another isn’t extra—it’s essential. Over time, this reinforces the idea that success is shared and that contribution is measured not just by what you produce but by how you help others succeed.
Why is a collaboration strategy important for an organization?
A collaboration strategy defines how individuals, teams, and departments work together to achieve shared goals. Without it, collaboration becomes fragmented, reactive, and inconsistent, leading to duplication of effort and missed opportunities. A clearly defined strategy sets expectations, defines roles, and establishes communication methods that streamline processes and reduce ambiguity.
First, it aligns teams toward common business objectives. Departments often operate with different agendas or workflows, and a strategy ensures coordination rather than conflict. This alignment enables better prioritization, decision-making, and execution, which directly impacts productivity and customer satisfaction.
Second, it promotes knowledge sharing and transparency. In many organizations, valuable insights remain siloed within teams. A strategy facilitates the exchange of expertise and feedback across functions, allowing ideas to evolve faster and solutions to emerge from diverse viewpoints.
Third, it reduces operational inefficiencies. A structured approach to collaboration helps eliminate redundant tools, unclear responsibilities, and misaligned expectations. It establishes norms for using communication platforms, file sharing, and collaborative decision-making, which prevents confusion and wasted time.
Fourth, it enhances adaptability. Markets shift rapidly, and cross-functional collaboration becomes crucial during change. A strategic framework prepares teams to coordinate quickly during transitions such as digital transformation, mergers, or crises.
Lastly, it boosts employee engagement. People perform better when they understand how their work contributes to broader goals and when they collaborate in psychologically safe environments. A collaboration strategy fosters trust, clarity, and inclusion—three key drivers of employee satisfaction.
In sum, a collaboration strategy creates a shared framework for achieving results, reducing friction, and maximizing organizational agility. It’s not just a communication improvement plan—it’s a fundamental driver of business performance and innovation.
What challenges are expected in implementing collaboration strategies?
Implementing a collaboration strategy involves navigating structural, cultural, and operational hurdles. These collaboration challenges often emerge at the intersection of people, technology, and organizational expectations.
One common issue is resistance to change. Employees may feel threatened by new systems, workflows, or expectations around transparency and accountability. Without buy-in, even the most well-crafted strategy fails. Leaders must communicate the “why” behind the strategy and actively address concerns to ensure adoption.
Another challenge is tool overload. Many organizations introduce new platforms without retiring old ones, resulting in fragmented communication. This causes confusion, slows work, and undermines trust in the strategy. A careful audit and consolidation of tools is critical during implementation.
Cultural misalignment also creates friction. Teams accustomed to working independently may not easily shift to open collaboration. A strategy must address this through clear behavioral norms and tailored onboarding, especially in cross-functional or global teams with varied work cultures.
Role clarity is often overlooked. Collaboration fails when responsibilities are vague or overlapping. Without clearly defined decision rights and task ownership, collaboration turns into endless discussion with little action.
Measuring success can also be difficult. Organizations rarely establish clear KPIs for collaboration. Without benchmarks, it becomes hard to identify what’s working or where to improve.
Lastly, inconsistent leadership support undermines credibility. Leaders must model collaborative behaviors and reinforce the strategy in meetings, reviews, and rewards.
Addressing these challenges requires deliberate planning, honest feedback loops, and continuous adjustment—not just a one-time rollout.
What challenges can you face if you lack a collaboration strategy in place?
Not having a collaboration strategy in place can lead to inefficiencies and conflict, affecting both team performance and organizational growth. Projects may stall due to misaligned expectations, duplicated work, or unclear responsibilities. Employees waste time searching for information or waiting for decisions, slowing down execution.
Lack of a structured approach also creates communication silos. Departments become isolated, limiting cross-functional innovation and creating disconnects that impact the customer experience. Trust erodes as team members encounter inconsistent processes or receive conflicting instructions from different stakeholders.
In the absence of defined collaboration norms, accountability suffers. Work may be unevenly distributed, with some team members overburdened while others lack clear direction. This imbalance leads to frustration, disengagement, and reduced morale.
Additionally, technology tools often become misused or underutilized. Teams may rely on personal preferences rather than agreed-upon systems, which results in fragmented knowledge sharing and lost context.
Ultimately, the organization becomes reactive instead of proactive. Strategic goals take longer to achieve, adaptability declines, and internal confusion spills over into poor client or customer interactions.
What is the role of leadership in implementing an effective collaboration strategy?
Leadership sets the tone for how collaboration is perceived, prioritized, and practiced across the organization. Leaders must go beyond approving the strategy—they must actively shape and model it.
First, they articulate a compelling vision for collaboration that connects directly to business goals. This narrative helps teams understand why collaboration matters and how it contributes to success.
Second, leaders are responsible for removing barriers. Whether it’s outdated workflows, conflicting incentives, or underperforming tools, leadership must identify and resolve these friction points to enable smoother collaboration.
Third, they must lead by example. When leaders consistently use the recommended platforms, demonstrate cross-functional engagement, and openly share information, it signals that collaboration isn’t optional—it’s standard practice.
Fourth, leaders must build psychological safety. Encouraging feedback, acknowledging mistakes, and promoting inclusive discussions help teams collaborate without fear of judgment or failure.
Lastly, leadership must reinforce collaboration through recognition and accountability. Celebrating collaborative success, rewarding team outcomes, and tying performance reviews to shared goals ensure the strategy remains embedded in the culture.
In short, leadership isn’t just a support function—it’s the operational engine that drives effective collaboration.
How to measure the impact of collaboration strategies?
To measure collaboration strategy impact, combine quantitative metrics with qualitative feedback. Start by defining clear goals tied to collaboration—such as faster project completion, increased innovation, or improved cross-team engagement—and then track metrics that align with those goals.
Use productivity indicators like task completion rates, project timelines, or cycle times to evaluate execution efficiency. Monitor communication tool usage (e.g., messages sent, meetings held, document sharing activity) to assess platform engagement, but avoid assuming high volume equals effectiveness.
Survey employees regularly to gauge perceptions of collaboration quality. Focus on clarity of roles, ease of accessing information, inclusiveness in discussions, and transparency in decision-making. Qualitative feedback often uncovers pain points that data alone misses.
Collaboration network analysis can also reveal who collaborates with whom, how frequently, and whether certain teams or individuals are becoming isolated or overloaded. This helps optimize workflows and reduce bottlenecks.
Finally, track outcome-based metrics like customer satisfaction, employee engagement, or innovation pipeline growth, especially in projects that require extensive collaboration.
The key is to measure what matters—not just activity, but progress toward strategic goals enabled by collaboration.
What are the best tools that support implementing a collaboration strategy?
The best collaboration tools align with your team’s workflows, communication preferences, and security needs. No single platform fits all use cases, but commonly used categories include:
- Project management tools like ProofHub, Asana, Trello, or ClickUp for tracking tasks and deadlines.
- Communication platforms like Slack or Microsoft Teams are used for real-time messaging and cross-functional discussions.
- Document collaboration tools such as Google Workspace or Notion for co-editing and organizing knowledge.
- Video conferencing tools like Zoom or Google Meet to facilitate face-to-face interaction.
- File sharing and storage platforms such as Dropbox or OneDrive for version control and access management.
Choose tools that integrate well with one another and support both synchronous and asynchronous work. Prioritize user adoption and training to maximize their effectiveness.
How often should you review your collaboration strategy?
You should review your collaboration strategy at least twice a year, or more frequently during periods of organizational change. A biannual cadence allows you to assess alignment with evolving business goals, address emerging bottlenecks, and adapt to new technologies or team structures.
Quarterly pulse checks, such as short surveys or cross-functional feedback sessions, can complement formal reviews. These help catch early signs of misalignment or underperformance before they escalate.
Also, review your strategy immediately after major events like mergers, leadership changes, remote work shifts, or tool rollouts. These moments often introduce new collaboration dynamics that require realignment.
Ultimately, the frequency should match your business’s pace. Fast-moving environments may demand more agile, ongoing adjustments, while stable organizations can rely on structured semiannual reviews.
Can organizational structure impact collaboration strategy?
Yes, organizational structure directly affects how collaboration strategies function. Hierarchical structures often introduce communication delays, with approvals and decisions flowing through multiple layers. In such environments, a collaboration strategy must focus on clarifying escalation paths and empowering cross-level communication.
In contrast, flat or matrixed structures offer more direct interaction across functions but can suffer from ambiguity in decision rights. Collaboration strategies in these setups must prioritize role clarity, task ownership, and conflict resolution mechanisms.
Additionally, decentralized organizations need localized collaboration norms that still align with central objectives. Remote or distributed teams require more emphasis on asynchronous communication and documentation practices.
Ultimately, the structure determines the channels, speed, and scope of collaboration. A one-size-fits-all approach won’t work—your collaboration strategy must adapt to how your organization is built.
Can collaboration strategies differ from team to team?
Yes, collaboration strategies should differ across teams based on their goals, structure, and work styles. A product development team may need iterative workflows, frequent stand-ups, and technical documentation, while a marketing team may prioritize campaign alignment, creative reviews, and asset sharing.
Factors like team size, time zones, dependencies, and decision-making autonomy all influence how collaboration should be structured. For instance, distributed teams may rely more on asynchronous updates, while colocated teams may benefit from informal huddles.
A centralized collaboration framework should guide consistency, but allow enough flexibility for teams to tailor their approach. This balance ensures strategic alignment without stifling team-level effectiveness.







